Overthewire
OverTheWire Monxla Part 3
Continuing from the last post, we are now logged in as a user. The next step on the PDF from the agent, that we can access, is the Notes Service.
I started analyzing the source code, and noticed that the text that says “yes” or “no” in the table is actually an image being …
OverTheWire Monxla Part 2
In the previous post, I showed how to get the PDF that outlines the services running on the Monxla VM image. This article will continue where that one left off.
Firstly, the PDF explains that there are 2 virtual hosts enabled on the machine. To configure my machine for these virtual hosts, I added …
OverTheWire Monxla Part 1
I had a twitter follower recently inform me that OverTheWire had a new wargame up and running. I was immediately excited and downloaded it. Several days later, I actually was able to start tinkering with it.
I booted up the image, and proceeded to do some preliminary nmap scans. I found a few …
OverTheWire Natas Level …
Up until now, none of the OverTheWire Natas challenges really gave me that much of an issue. This one however, took me a couple hours to complete. Level 15 is a fun blind sql-injection vulnerability.
It starts out with a username check dialog, which pretty much only gives you a binary value as to …
OverTheWire Natas Level …
The next level of the OverTheWire Natas wargame is Level 14, which introduces SQL Injection, a very popular subject as of late.
The level starts out with a login dialog.
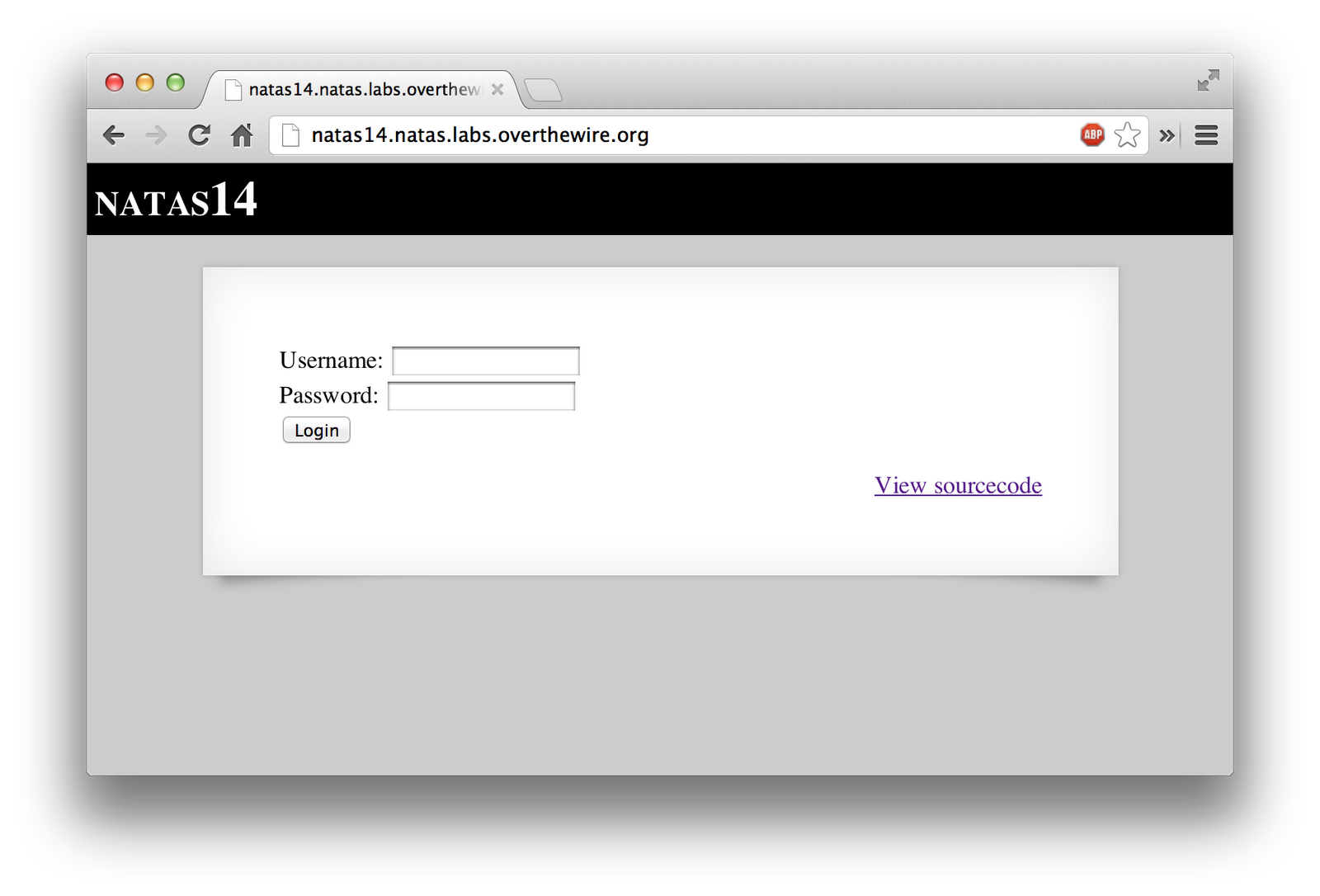
The source code is fairly straight forward. It’s doing a basic authentication query. It however, does have a handy …
OverTheWire Natas Level …
Level 13 of OverTheWire’s Natas wargame is extremely similar to Level 12. The only difference now, is that it’s validating that the file is in fact an image. This however is flawed, as exif data can be faked.
It starts out with a similar upload prompt as last time.
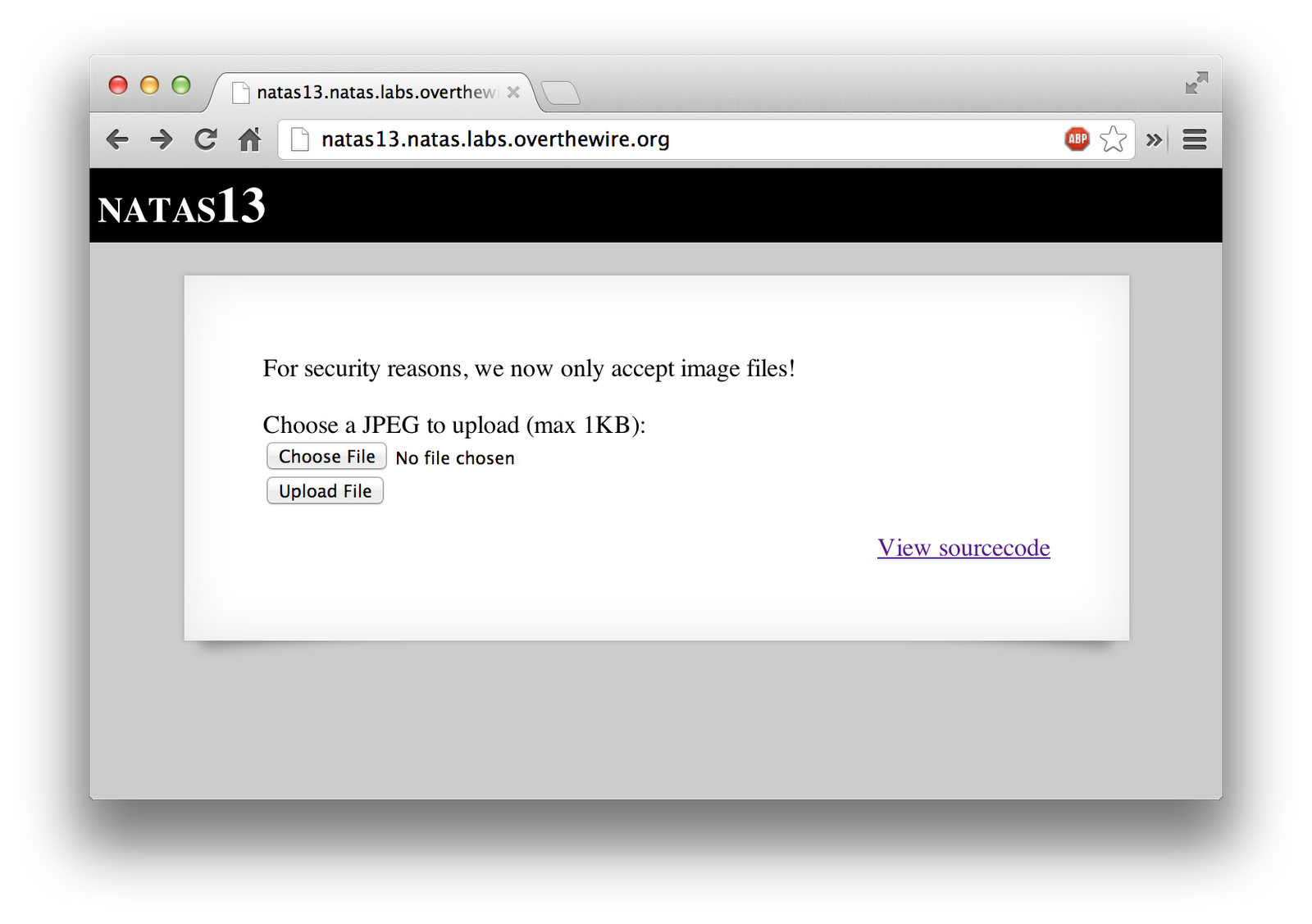
The source code is …